Windows Red Team Lab Review
Students will be given remote desktop access to student machines that are connected to the Windows Active Directory with least privilege, and privilege escalation on student machine is part of challenge.
Intro
Red Team generally is different with Penetration Test, Red Team is very offensive and should be performed as stealthy as possible. Readteaming is not determined by scope, but based on goals, such as compromise high-level e-mail or device, compromise Domain Controllers of an organization, and more. To be able to do that, the attacks should not meet any restrictions.
Red teaming should be done when an organization already has a very good security perimeter in securing their assets and have a team that monitors the attacks directly (Blue Team). Here Red Team will test the response of the Blue Team to minimize the security gap and provide recommendations for the Blue Team. Please note that this is not a matter of who wins and who loses, but it is done to make the organization have a better security perimeter. Also, it will make the Blue Team works (detecting real world attacks) better.
But here I don’t want to explain the details of Red Team, I just want to give a review on the Windows Red Team Lab by Pentester Academy.
Background
I was simply curious about Red Teaming, and that’s become my motive on why I took Windows Red Team Lab from Pentester Academy.
Windows Red Team Lab
Pentester Academy provides three options to take this lab for 30 Days, 60 Days, or 90 Days including course material and VPN connections to their labs. And after the lab ends, there will be a 48-hour exam including sending a report. If you pass the exam you will get a CRTE (Certified Red Team Expert).
Training Labs
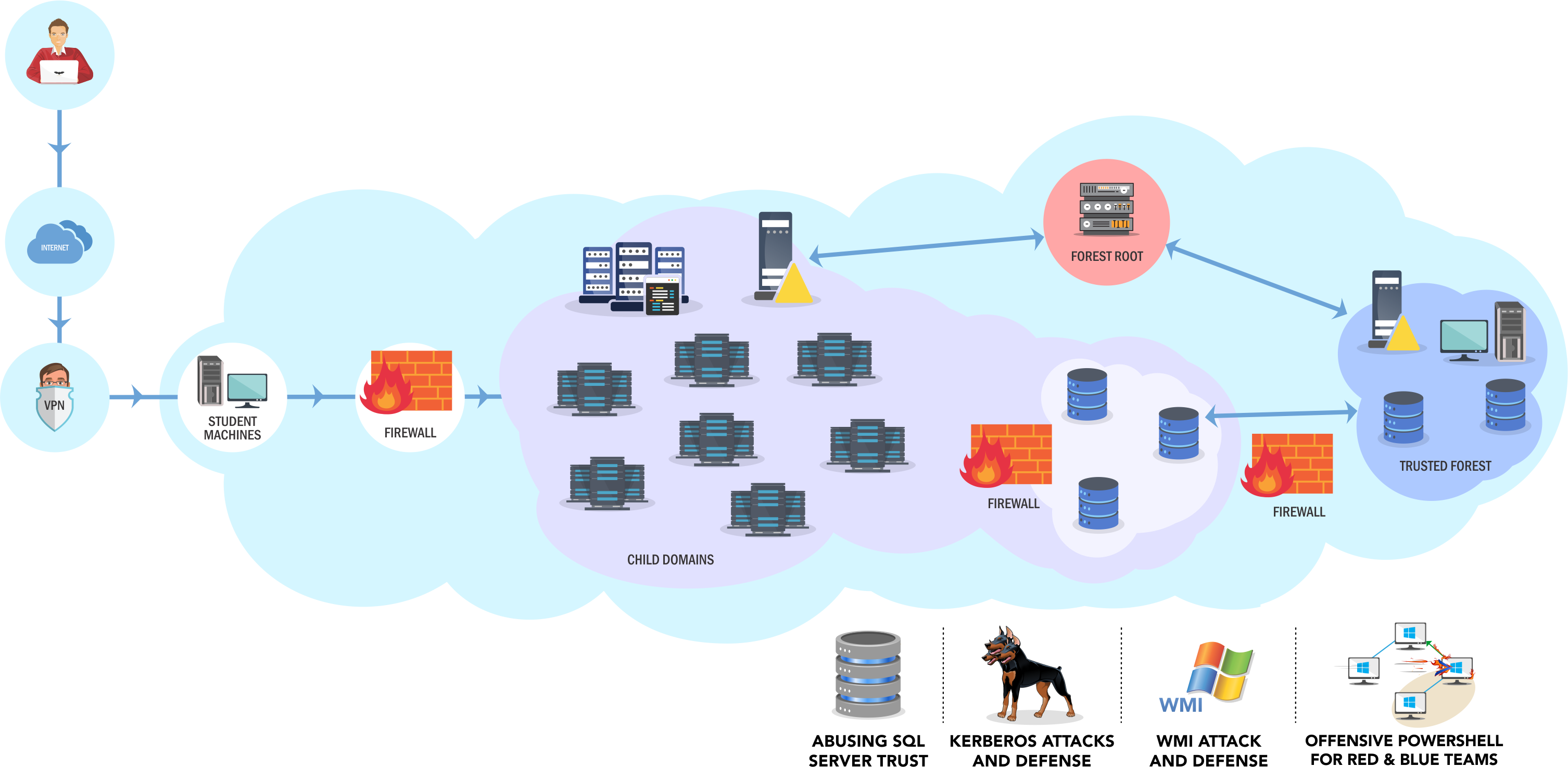
Students will be given remote desktop access to student machines that are connected to the Windows Active Directory with least privilege, and privilege escalation on student machine is part of challenge. After you successfully escalate your privilege on your machine, you can upload malicious binaries or tools that you need to perform enumeration or attacking further.
The network in the lab will be exactly look like this.

In this lab I learned a lot of new things, such as how-to Windows Kerberos works and utilizes misconfiguration to gain access to services, how to bypass whitelisted and constrained mode on PowerShell in an unusual way, exploiting misconfiguration of SQL Server and more. The attack will all be done using PowerShell.
There is a choice when working on this lab, the first given lab is set to the hard level, but student can ask to reduce the level of difficulty. On the hard level the student machine cannot connect to any ports on our laptop/PC. During the experience, I choose hard level to give me more challenge and it should be fun.
Thanks to this course and lab, I can now utilize and carry out attacks by only using PowerShell, netcat as listener, and some other binaries such as Mimikatz and Kekeo. No Metasploit, Empire, Cobaltstrike or another C2 needed.
Students are also required to submit as many flags as possible. Flags that must be obtained are 60 flags in total.
Exam Labs
The exam lab has 8 servers which are spread across forests. It must be done in 48 hours include building the reports. You must manage your time very well!
3 boxes must be compromised in order to pass this exam but only with top quality report you can pass the exam. If you can compromised more than 3 boxes you can send a report with average quality.
The key to passing this exam is enumeration and try harder.
Conclusion
I’ve never have time to learn Active Directory before, the training material and lab provided was very helpful for me to be able to learn from zero. Though I know there are several labs other than Windows Red Team Lab such as Rastalabs (Hack the Box).
Final words, Windows Red Team Lab is very fun and very challenging, thank you Nikhil Mittal for designing this awesome lab, looking forward to your new lab challenges.
